Viewing Vulnerabilities
Vulnerabilities are failures to control an IT asset that makes it vulnerable to a threat and can lead to a breach of confidentiality, lack of integrity or availability of this asset.
Vulnerabilities can be imported from national databases or managed with appropriate vulnerability management tools.
Accessing vulnerabilities
To access vulnerabilities:
2. From the inventory page, click Threats and Vulnerabilities > Threats and Vulnerabilities.

You can also access vulnerabilities by vulnerability type. See
"Source".
Creating a vulnerability type
To create a vulnerability type:
1. From the inventory page, click Threats and Vulnerabilities > Vulnerabilities by Vulnerability Type.
2. Right-click on the root of the "Threats and Vulnerabilities" tree and select New > Vulnerability Type.
The vulnerability type appears in the tree.
Characteristics of vulnerabilities
Threat
A threat can potentially exploit a vulnerability.

A vulnerability can only be associated with a single threat.
Type of vulnerability
Vulnerability types organize vulnerabilities into different categories (e.g.: Software, Organization, Site-Location, etc.).
Original release date
The release date is the date at which a vulnerability was described for the first time.
This characteristic is optional. It can be useful when importing from a third-party source.
Last modification date
The last date of modification is the date at which the vulnerability was modified.
This characteristic is optional. It can be useful when importing from a third-party source.
Source
Vulnerabilities are made available and updated regularly by national and standards organizations, for example:
• NIST (National Institute of Standards and Technology)
• CVE (Common Vulnerabilities and Exposures)
• ISO (ISO 27000)
Status
• Potential
• Detected
• Remediated
• Closed
Vulnerability score
• Low
• Medium
• High
Scope of vulnerabilities
The scope of vulnerabilities is made up of two sections:
• assets
• deployed assets

In practice, either one or the other is used, according to the inventory (deployment types)
Vulnerable IT assets
• Applications

A business application is a set of software tools that make up a consistent whole from a software development viewpoint and with respect to functionalities supplied to users.
• Software technology

A software technology is a basic component necessary for operation of business applications.
Vulnerable deployed IT assets
• Software installation

A software installation is the deployment of an application with a view to using it on a given site.
• Deployed technology

A software technology is a basic component necessary for operation of business applications.
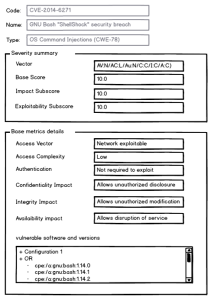
CVSS assessment
The Common Vulnerability Scoring System (CVSS) is a standardized assessment system for the criticality of vulnerabilities according to objective and measurable criteria.
CVSS is a scoring system enacted by the National Institute of Standards and Technology (NIST) in the United States and is a de facto standard.

This data is imported using third-party tools and is not entered in
HOPEX IT Risk Management.
Examples of data
Reports concerning vulnerabilities